Secure Corporate Communications a Using Private APN Network
For modern organizations, the internet is both a blessing and a curse: While this technology provides employees with any information they may need to perform their work, it is also a significant vulnerability.
Enterprises routinely experience hacks, attacks, and other security breaches due to insecure corporate communications. These incidents cause major problems for organizations, who must contend with the fallout on several fronts.
1Why corporate communications needs to be secured
Reputational damage
The media frequently covers stories of companies that suffer from security breaches. Even if the company takes immediate action, the organization will still suffer reputational damage. Why should customers trust the organization with their business if it cannot even protect their systems and data?
Under this assumption, users may close their accounts, and clients may end their contracts. Potential customers will look elsewhere, prioritizing companies that can solve their pain points and secure their data.
Operational chaos
Dealing with a security incident is operationally intensive. Company leaders must investigate the breach, determine how to shore up the weakness, and execute this plan within hours or days. The company will be scrambling to solve a problem it should have already long anticipated and prevented.
This kind of incident response is operationally intensive. It requires close coordination from multiple company departments, wastes hundreds of man-hours, and removes focus from the organization’s strategic priorities. Addressing the vulnerabilities in corporate communications in advance would have taken a fraction of the same resources.

Financial costs
The most significant impact of any security incident is the financial costs, which may be staggering. Businesses will have to pay for the labor it takes to fix the problem, including employees and any third-party service providers, the price of any new cybersecurity solution, and any penalties leveraged upon them by regulators.
There will also be significant indirect costs. Organizations will lose potential business, brand equity in the marketplace and even human capital: Current employees may leave the company due to the incident, and applicants may opt to apply elsewhere. A breach due to insecure corporate communications is expensive.
2The dangers of using a public APN instead of a dedicated APN
A major vulnerability in corporate communications is how employees access the internet. Most mobile devices connect to the internet through a public access point name (APN). Once the APN is authenticated, it will provide instructions to the mobile network operator (MNO) about the IP address, security configurations, and network being accessed.
Unfortunately, public APNs do not have the security necessary for secure corporate communications, exposing businesses to many potential threats.
Sniffing
Traffic on public APNs is typically not encrypted. As a result, hackers can use sniffing tools that decode packets of data to steal sensitive information, such as company credit card numbers or administrator credentials. This threat is especially grave in industries where all information by nature is sensitive, such as healthcare or finance.

Man-in-the-middle attack
Like sniffing, man-in-the-middle attacks intercept data between parties, such as internet traffic, emails, or instant messages. While the attacker can listen for confidential information, it can also alter the data, which is potentially more dangerous. For example, a man-in-the-middle attacker can change the account number on an invoice to their own so that the company inadvertently pays them rather than the vendor.
Unauthorized computer access
Even employees with a technical background may need to learn how to deny access to specific files or folders. When these employees use a public APN, hackers may gain access to these unsecured files or folders. Unauthorized access to a mobile device may also yield sensitive information to hackers.
Spoofed APNs
Attackers may set up public APNs similar in name to legitimate APNs. This trap will trick employees into connecting to the spoofed APN, compromising their security. Attackers can monitor the traffic for sensitive information, hijack the session, and even push malware to the mobile device.
While these are just some of the many threats posed by using a public APN, the critical point should be emphasized: They do not meet the strict security needs of corporations.
3The security of a dedicated APN
The more appropriate solution is a private access point name, which allows organizations to build networks customized to their unique security needs and appetite. Employees then connect to the private APN, which routes traffic to the internet first through the company network and maximizes security through different features.
An APN private network has a company firewall
Corporate communications are much safer because the company can set up a secure tunnel for this traffic, one complete with a firewall. The firewall authenticates all data entering the company network, which limits a variety of cyber threats, including malware, denial-of-service attacks, spam, and more.
Just as crucially, the firewall minimizes the ability of employees to make risky behaviors online. They will be prevented from visiting suspicious websites, downloading dangerous files, or granting access to malicious software. At a time when employees can often be the weakest link, deploying guardrails for safe internet usage is essential for any enterprise.
A dedicated APN has a fully customizable environment
Anyone can connect to a public APN, so they present many cybersecurity threats. With a private APN, companies can fully customize which devices - and under what circumstances - they can connect to the company network.
For example, a company may use a dedicated APN to limit access to devices within a specific IP address range. This customization would prevent access from devices that outside the given range that may represent a threat (i.e. a malicious actor based in another geography from where the company is located).
A dedicated APN can power Multi-factor authentication
The golden standard in authentication is multi-factor authentication, which requires two or more forms of authentication, such as login credentials and a code sent to an email or one provided by an authenticator app.
A private APN network will enable companies to turn on multi-factor authentication and design it to meet their operational needs best. Multi-factor authentication will make it substantially difficult for third parties to gain unauthorized access to the organization’s mobile devices or overall network.
4How an MDM can operationalize an APN private network
While a dedicated APN is beneficial, it is also resource-intensive. IT teams would have to individually configure each mobile device, which is a drain on their time and effort that could be better spent on other activities.
Fortunately, enterprises can more easily manage their organization’s private APN network with an MDM solution like AirDroid Business. The first significant advantage is scale. Rather than individually configure each mobile device, IT teams can determine APN settings company-wide or in different batches of phones as part of its Policy feature.
The second advantage is speed. The interface of an MDM is intuitive, allowing IT professionals, even those with minimal experience in private APNs, to determine the correct settings for the company or group. Choosing different settings is as easy as assigning a created APN to a configuration file and customizing the different APN options, such as username and password.
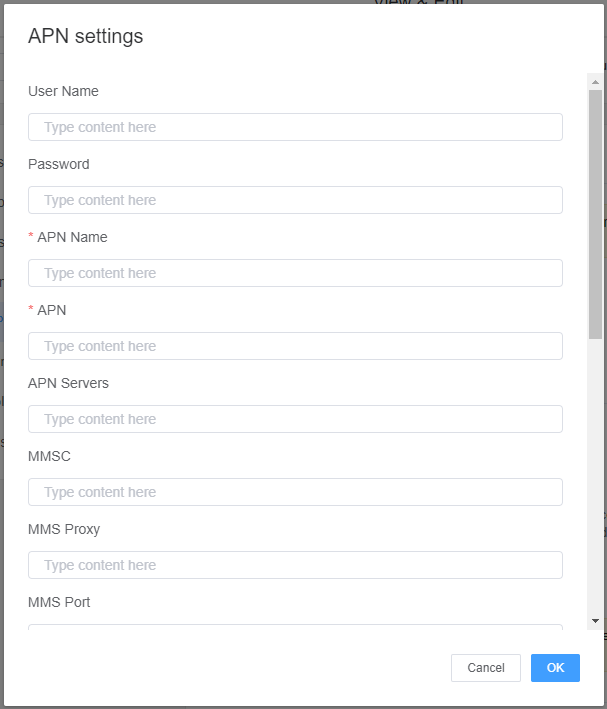
The final advantage is granularity. Because IT teams can set different APN options per configuration file, they have greater flexibility in administering their private network. For example, one company may have stricter APN settings for rank-and-file employees but give more freedom to tenured executives.
Managing a dedicated APN is substantially easier through an MDM, which already provides many other benefits ideal for an enterprise.
5Protecting your company with a APN private network
The business environment is changing. Companies can no longer play it fast and loose with their communications. Stakeholders across the business ecosystem, including employees, customers, clients, suppliers, and partners, increasingly prefer organizations that prioritize security.
While many best practices are involved in securing corporate communications, one of the simplest is implementing a private APN network instead of a public one. A public APN exposes organizations to various security threats, such as man-in-the-middle attacks, leading to reputational damage, financial losses, and operational chaos.
A dedicated APN is a far better solution for businesses. Private APNs are much more secure because companies can route traffic through a firewall, fully customize the work environment, and require multi-factor authentication. It would be impossible for any solution to eliminate all threats, but a private APN network will dramatically minimize the possibility of a cybersecurity incident.
Individually configuring a dedicated APN for every mobile device is difficult. To simplify this task, enterprises can choose an MDM like AirDroid Business. These solutions help organizations set their private APN settings in batches, customize them through an intuitive interface, and deploy them to the organization’s mobile devices quickly. When paired with a MDM, a private APN is even more powerful, allowing organizations to protect their mobile devices and network with greater speed, scale, and efficiency.
Beginner's Guide for AirDroid Business
This is a comprehensive guide for AirDroid Business mobile device management (MDM) solution. Learn how you can simplify IT operations with device monitoring, provisioning, alerting, remote control, Kiosk Mode, automatica app update, and more.






Leave a Reply.